Anesthesia Practices May Be Subject to the Phase 2 HIPAA Audits
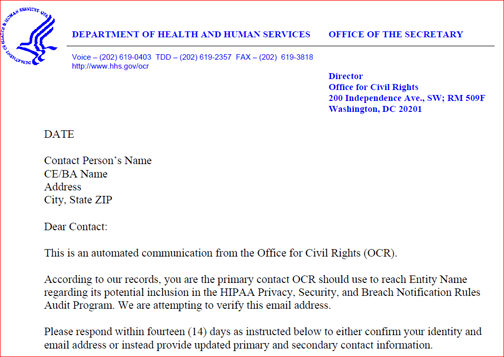
If you receive a letter by email that begins like this:
You should respond within the 14 days mentioned in the letter. Congratulations; you are participating in Phase 2 of the HIPAA Audit Program.
With this letter, OCR is seeking just to identify contacts to create a pool of HIPAA-covered entities (CEs) and their business associates (BAs) for possible audits. In the next step, OCR will transmit a pre-audit questionnaire to gather data about the size, type, and operations of CEs and their BAs. These data will then be used with other information to create potential audit subject pools. Eventually more than 200 entities will face audits in Phase 2 of the HIPAA Audit Program, which will primarily be desk audits, although some on-site audits will also be conducted.
Phase 1 of the HIPAA Audits
HIPAA established national standards for the privacy and security of protected health information. The Health Information Technology for Economic and Clinical Health Act (HITECH) established breach notification requirements to provide greater transparency for individuals whose information may be at risk. HITECH requires the OCR to conduct periodic audits of covered entity and business associate compliance with the HIPAA Privacy, Security and Breach Notification Rules.
In 2011 and 2012, OCR implemented a pilot audit program to assess the controls and processes implemented by 115 covered entities to comply with HIPAA’s requirements. The 979 "findings and observations” from Phase 1 were released in 2013. OCR also conducted an evaluation of the effectiveness of the pilot program. Drawing on that experience and the results of the evaluation, OCR is implementing Phase 2 of the program.
Phase 2
The 2016 Phase 2 HIPAA Audit Program was announced at the 24th National HIPAA Summit in the District of Columbia on March 21, 2016. In Phase 2, OCR will review the policies and procedures adopted and employed by CEs and their BAs to meet selected standards and implementation specifications of the Privacy, Security and Breach Notification Rules. According to the agency,
OCR uses the audit program to assess the HIPAA compliance efforts of a range of entities covered by HIPAA regulations. The audits present an opportunity to examine mechanisms for compliance, identify best practices, discover risks and vulnerabilities that may not have come to light through OCR’s ongoing complaint investigations and compliance reviews, and enable us to get out in front of problems before they result in breaches. OCR will broadly identify best practices gleaned through the audit process and will provide guidance targeted to identified compliance challenges.
The first series of desk audits will focus on CEs; the second round of audits will target BAs. By December 2016, all desk audits should be completed.
OCR has posted information on a number of practical questions on its website, including the following:
- Who is responsible for making sure that the entities to which OCR sends Phase 2 emails actually see the communications? You are. OCR has stated that its communications “will be sent via email and may be incorrectly classified as spam. If your entity’s spam filtering and virus protection are automatically enabled, we expect you to check your junk or spam email folder for emails from OCR; OSOCRAudit@hhs.gov.”
- Who Will Be Audited? Every covered entity and business associate is eligible for an audit. These include covered individual and organizational providers of health services; health plans of all sizes and functions; health care clearinghouses; and a range of business associates of these entities.
- On What Basis Will Auditees Be Selected? Sampling criteria for auditee selection will include size of the entity, affiliation with other healthcare organizations, the type of entity and its relationship to individuals, whether an organization is public or private, geographic factors, and present enforcement activity with OCR. OCR will not audit entities with an open complaint investigation or that are currently undergoing a compliance review.
- How Will the Selection Process Work? Once entity contact information is obtained, a questionnaire designed to gather data about the size, type, and operations of potential auditees will be sent to covered entities and business associates. As a part of the pre-audit screening questionnaire, OCR is asking that entities identify their business associates. We encourage covered entities to prepare a list of each business associate with contact information so that they are able to respond to this request. OCR will conduct a random sample of entities in the audit pool. Selected auditees will then be notified of their participation.
If a covered entity or business associate fails to respond to information requests, OCR will use publicly available information about the entity to create its audit pool. An entity that does not respond to OCR may still be selected for an audit or subject to a compliance review.
- How Will the Audit Program Work? The first set of audits will be desk audits of CEs followed by a second round of desk audits of BAs. These audits will examine compliance with specific requirements of the Privacy, Security, or Breach Notification Rules and auditees will be notified of the subject(s) of their audit in a document request letter.
The third set of audits will be onsite and will examine a broader scope of requirements from the HIPAA Rules than desk audits. Some desk auditees may be subject to a subsequent onsite audit.
The audit process will employ common audit techniques. Entities selected for an audit will be sent an email notification of their selection and will be asked to provide documents and other data in response to a document request letter. Audited entities will submit documents on-line via a new secure audit portal on OCR’s website. There will be fewer in person visits during these Phase Two audits than in Phase One, but auditees should be prepared for a site visit when OCR deems it appropriate. Auditors will review documentation and then develop and share draft findings with the entity. Auditees will have the opportunity to respond to these draft findings; their written responses will be included in the final audit report. Audit reports generally describe how the audit was conducted, discuss any findings and contain entity responses to the draft findings.
- What is the General Timeline for an Audit? In the coming months, OCR will notify the selected covered entities through email about their selection for a desk audit. The OCR notification letter will introduce the audit team, explain the audit process and discuss OCR’s expectations in more detail. In addition, the letter will include initial requests for documentation. OCR expects covered entities that are the subject of an audit to submit requested information via OCR’s secure portal within 10 business days of the date on the information request. All documents are to be in digital form and submitted electronically via the secure online portal.
After these documents are received, the auditor will review the information submitted and provide the auditee with draft findings. Auditees will have 10 business days to review and return written comments, if any, to the auditor. The auditor will complete a final audit report for each entity within 30 business days after the auditee’s response. OCR will share a copy of the final report with the audited entity.
Similarly, entities will be notified via email of their selection for an onsite audit. The auditors will schedule an entrance conference and provide more information about the onsite audit process and expectations for the audit. Each onsite audit will be conducted over three to five days onsite, depending on the size of the entity. Onsite audits will be more comprehensive than desk audits and cover a wider range of requirements from the HIPAA Rules. Like the desk audit, entities will have 10 business days to review the draft findings and provide written comments to the auditor. The auditor will complete a final audit report for each entity within 30 business days after the auditee’s response. OCR will share a copy of the final report with the audited entity.
- What Happens After an Audit? Audits are primarily a compliance improvement activity. Generally, OCR will use the audit reports to determine what types of technical assistance should be developed and what types of corrective action would be most helpful. Through the information gleaned from the audits, OCR will develop tools and guidance to assist the industry in compliance self-evaluation and in preventing breaches. The technical assistance and “promising practice” that OCR generates will also assist covered entities and business associates in improving their efforts to keep health records safe and secure.
Should an audit report indicate a serious compliance issue, OCR may initiate a compliance review to further investigate.
- Will Audits Differ Depending on the Size and Type of Participants? The audit protocols—which have not yet been made public—are designed to work with a broad range of CEs and BAs, but their application may vary depending on the size and complexity of auditee.
- Who is Responsible for Paying the On-Site Auditors? The Department of Health and Human Services, not the CEs or their BAs, is responsible for the costs of the whole audit program.
HIPAA security has become a very hot issue because of the exploding number and variety of cyber-crimes committed against healthcare institutions and patients. From October of 2009 through March 2016 the Secretary of HHS’ Breach of Unsecured Protected Health Information Portal documented over 157 million individuals who were affected by PHI breaches.
Until recently, most breaches were the result of employee errors such as opening emails containing malware, failing to encrypt data and losing media or laptops. Malicious activity by third parties has now overshadowed internal carelessness, not least because of the sophistication of hackers and other criminals.
Last month, OCR announced a pair of settlement agreements totaling nearly $5.5 million with the Feinstein Institute for Medical Research in New York and North Memorial Health Care in Minnesota to settle possible HIPAA violations.
The Feinstein Institute had filed a breach report with OCR in 2012 reporting a laptop stolen from an employee’s car. The laptop contained the electronic protected health information (ePHI) of about 13,000 patients and research participants, including names, dates of birth, diagnoses and medications. OCR’s investigation showed that the Feinstein Institute “lacked policies and procedures for authorizing access” to ePHI by its workforce members. OCR also found that the Institute “failed to implement safeguards to restrict access to unauthorized users, and lacked policies and procedures to govern the receipt and removal" of the organization’s laptops that contained ePHI. The lack of policies and safeguards cost the Institute $3.9 million.
North Memorial Health Care agreed to pay $1,550,000 to settle charges that it had potentially violated HIPAA “by failing to enter into a business associate agreement with a major contractor and failing to institute an organization wide risk analysis to address the risks and vulnerabilities to its patient information,” according to OCR’s statement. This investigation began when OCR was notified that an unencrypted, password-protected laptop had been stolen from a business associate’s workforce member’s locked vehicle, potentially affecting the electronic protected health information (ePHI) of 9,497 individuals.
The problem of healthcare data breaches is growing all the time and it can affect any of us. Eighty-one percent of healthcare executives say that their organizations have been compromised by at least one malware, botnet, or other cyber attack during the past two years, and only half say they feel that they are adequately prepared in preventing attacks, according to a 2015 KPMG healthcare cybersecurity survey. (Mace S. Living in the Healthcare Data Breach Era. HealthLeaders Magazine online, March 2016.)
Preparing to prevent cyber attacks and preparing for a possible OCR audit both begin with a HIPAA security risk assessment. Timothy McCrystal, Esq., a healthcare partner at Ropes & Gray, advises practices that receive a contact-identification letter from OCR “to pull out their current HIPAA security risk assessment (which typically produces a work plan) and follow up on open areas. ‘Now is the time to be spending internal time and resources remediating those issues.’” (Conn J. New HIPAA Audits Will Target Healthcare Industry's Business Partners. Modern Healthcare online, March 21, 2016.)